Is iPhone Harder to Hack Than Android? A Security Compare
Explore whether is iphone harder to hack than android by comparing security models, updates, app vetting, and user practices. Practical guidance from Phone Tips Pro.

According to Phone Tips Pro, while no platform is invulnerable, iPhone devices typically offer stronger default security due to a controlled ecosystem, rapid updates, and rigorous App Store screening. For many users, this makes is iphone harder to hack than android in everyday use. However, user behavior and timely patching remain decisive factors in overall risk.
is iphone harder to hack than android: framing the question
The short answer is nuanced. The question is loaded with assumptions about software, hardware, and user behavior. is iphone harder to hack than android? On balance, iPhones benefit from a tightly controlled ecosystem, more uniform security updates, and a reputation for disciplined patching, which tends to reduce many common attack vectors. According to Phone Tips Pro, these factors contribute to a stronger baseline security posture for iPhone users in typical scenarios. But the reality is not binary: a well-targeted attack or a misconfigured device can compromise either platform. In this article, we compare security models, update processes, and practical steps you can take to minimize risk across both ecosystems. We’ll also outline concrete hardening measures so you can make an informed choice based on your risk tolerance and usage patterns. The goal is to provide an objective framework for evaluating the claim once and for all, rather than promising an absolute, one-size-fits-all answer.
The security models: iOS vs Android design choices
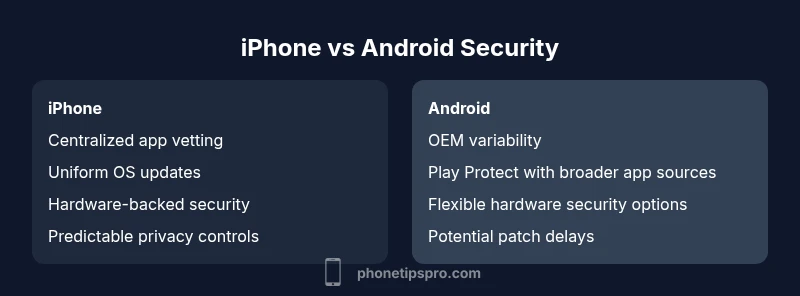
A fundamental difference between the two platforms lies in their base security models. iOS emphasizes a closed, sandboxed environment, rigorous app vetting, and a centralized update channel. The OS enforces strict permissions, background task limits, and mandatory cryptographic protections that apply across all devices. Android, by contrast, runs on a broad range of devices with varying OEM skins, updater schedules, and app provenance. While Google has strengthened Play Protect and system-level security features, the ecosystem remains more heterogeneous. This contrast influences how threats propagate and how quickly patches reach users. From the perspective of an attacker, an attack that works on one Android device may not work on another because of hardware or vendor-specific mitigations. For iPhone users, the uniform model reduces many chances of exploitation, but it does not erase risk entirely. For those who rely on third-party app sources or sideloading, the differences become even more pronounced. Understanding these structural choices helps frame the later discussion about real-world risk and best-practice mitigation.
Update cadence, patching, and app vetting
Software updates are the heartbeat of platform security. On iPhone, Apple generally delivers OS updates to a large majority of devices within a short window, and updates come directly from Apple with limited carrier or OEM interference. This accelerates the deployment of security patches and reduces the window during which known vulnerabilities can be exploited. App vetting refers to the process by which apps are reviewed before appearing in the App Store, with automated checks and human review. This model lowers malware risk by reducing the chance of malicious apps reaching users. Android uses a combination of Play Protect scanning and option to install apps from outside the Play Store in some markets; while this flexibility is beneficial for power users, it also introduces higher risk if apps come from untrusted sources or if devices do not receive timely OS updates. In practice, the speed and reliability of patch delivery depend on device age, carrier, and OEM policies. For security-conscious users, this means prioritizing devices and settings that minimize exposure to unvetted apps and delayed patches.
Attack surfaces: hardware, software, and supply chain
Attack surfaces are a function of both design and usage. Hardware features like Secure Enclave, Touch ID/Face ID, Secure Boot, and hardware-backed keychains provide a foundation that resists tampering. Apple designs integrate these elements with iOS to enforce cryptographic keys and biometric verification at a system level. Android devices vary; some vendors implement strong hardware security modules, while others rely more on software protections. Supply chain risk is another factor: tampering or pre-installed malware at the manufacturing stage is a theoretical risk for any consumer device, though modern supply chain safeguards are robust across major brands. The point is not to claim perfect safety, but to recognize where risk is concentrated: default security posture, user choices, and timely updates all shape how likely an attacker can compromise a device. In practice, people who disable features or root devices on Android may inadvertently undermine the security benefits of the platform.
Real-world threats and expert perspectives
While lab tests and threat reports provide insight, real-world risk depends on user behavior and ecosystem characteristics. Malware distribution for iOS remains comparatively limited due to App Store vetting, but phishing, credential theft, and exploit chains do occur. Android faces broader exposure to malware in certain markets where sideloading is common or where OEM updates lag behind the base Android version. Experts emphasize layered defenses: strong authentication, regular OS updates, minimized permissions, and careful app sourcing. Phone Tips Pro Analysis, 2026 highlights that no platform is immune; the best protection comes from a consistent security routine and awareness of social-engineering tactics. For both platforms, enabling two-factor authentication, using hardware-backed keys when available, and maintaining current firmware significantly reduces exposure to high-severity flaws.
User behavior, privacy controls, and permissions
Security posture is only as strong as the choices users make. On iPhone, you can easily review app permissions, limit access to location and microphone, and enable privacy labels to understand data usage. On Android, the same principle applies, but control granularity and the number of settings can vary by OEM and version. The most impactful habits include enabling automatic updates, using a strong passcode, turning on Find My iPhone or Find My Device, and regularly auditing installed apps. Also consider enabling lock-screen protections, such as requiring a passcode after reboot, and using biometric unlock with a timer that reduces exposure if your device is stolen. Even with robust defaults, phishing remains a top threat—education and skepticism in click behavior are critical across platforms.
Hardening: iPhone-specific steps
To reduce risk on iPhone, focus on layering defenses: keep iOS updated, enable two-factor authentication for Apple ID, and set a strong passcode. Turn on Find My iPhone and Activation Lock, enable iCloud Keychain, and review app permissions regularly. Consider enabling two-factor authentication for critical accounts, using a hardware security key when available, and avoiding risky network connections on public Wi-Fi. Finally, minimize reliance on encryption-only protections and pair them with good password hygiene and regular backups.
Android hardening: how customization can backfire and how to mitigate
Android’s openness invites flexibility but also extra care. Prioritize devices from reputable manufacturers with consistent security patches, disable unknown sources, and keep Play Protect enabled. Limit app permissions, install apps only from trusted sources, and use screen locks and biometric protection. Regularly back up data and apply monthly security patches where possible. If you must customize, choose well-supported ROMs and stay within a tested release cycle to reduce the risk of unpatched vulnerabilities.
Cross-platform best practices for security
Regardless of platform, adopt a shared security playbook: enable MFA, keep devices updated, review app permissions, and use encrypted backups. Use a VPN on public networks, avoid jailbreaking or rooting, and maintain separate, strong credentials for critical services. Regularly audit connected devices and permissions, and consider hardware-backed keys for sensitive accounts. These habits improve resilience whether you’re on iPhone or Android.
The decision framework: risk tolerance and use case
Your choice should reflect risk tolerance, data sensitivity, and usage patterns. If you handle highly sensitive work data, a controlled environment with strict update cycles may offer clearer risk management on iPhone. If you depend on device customization, enterprise mobility management, or a broader hardware ecosystem, Android may align better—provided you commit to disciplined updates and secure configuration. The right path balances usability with protective controls rather than pursuing a single universal rule.
Practical considerations and future trends
Looking ahead, both platforms are likely to emphasize hardware-backed security, faster patching, and improved identity protection. Apple will continue to expand hardware-rooted protections, while Android manufacturers will push for more uniform updates across devices. Staying informed through trusted sources and adherence to best practices will remain essential as the threat landscape evolves. In short, while the headline question is useful for framing risk, the real answer lies in ongoing, deliberate security hygiene across platform and user behaviors.
Comparison
| Feature | iPhone | Android |
|---|---|---|
| Security model | Centralized, controlled ecosystem | Fragmented ecosystem with OEM variability |
| App vetting | Mandatory App Store review | Play Protect + variable vetting; sideload risk |
| Update cadence | Uniform OTA updates from Apple | Patch delivery varies by OEM/carrier |
| Malware prevalence | Lower due to vetting | Higher in markets with sideloading |
| Patch adoption speed | Typically rapid | Depends on device and carrier |
| Privacy controls | Integrated, consistent privacy features | Varies by OEM/stock Android features |
| Customization freedom | Limited customization | High customization options |
| Total cost of ownership | Higher device cost, strong resale | Lower upfront cost, more varied long-term costs |
Positives
- Clear app vetting reduces exposure to malicious apps
- Tightly integrated security updates and patches
- Strong default privacy controls across many devices
- Predictable user experience with consistent security posture
Weaknesses
- Fragmentation in Android can slow patch deployment on some devices
- Less control for advanced users due to sandboxing and OEM skins
- Android malware diversity due to sideloading risk in some markets
- Higher user risk if devices are purchased from less reputable sources
iPhone generally offers stronger default security, making it harder to hack than Android for typical users.
iOS’s controlled ecosystem, timely updates, and strong app vetting create a robust baseline. Android’s openness introduces more variability, which can increase risk if patches and protections are not diligently applied. Your security outcome hinges on usage, updates, and careful app management across both platforms.
FAQ
Is iPhone harder to hack than Android in practice?
In practice, yes for many everyday users due to a more controlled ecosystem and faster, uniform updates. However, no device is immune, and user behavior plays a major role in risk. Malicious apps, phishing, and credential theft can affect either platform.
For most people, iPhone offers stronger default security, but always stay alert to phishing and weak passwords.
Can Android ever be as secure as iPhone?
Android can reach high security levels through careful device selection, timely patches, reduced app permissions, and disciplined user practices. Yet, fragmentation and variable patching can leave some devices more exposed than iPhones.
Android can be very secure if you manage updates and apps carefully.
What are the top attack vectors today?
Phishing and credential theft, outdated software, malicious apps from untrusted sources, and insecure Wi-Fi networks remain common threats across both platforms.
Watch for phishing and keep software up to date.
Do updates fix all security issues?
Updates fix known vulnerabilities and improve defenses, but new flaws can appear. Regular updates and good security hygiene remain essential.
Updates help a lot, but you still need good habits.
What should I do to secure my iPhone?
Use a strong passcode, enable two-factor authentication for Apple ID, enable Find My iPhone, review app permissions, and keep iOS updated. Consider a hardware security key for critical accounts.
Turn on security features and keep software up to date.
Is jailbreaking an iPhone a security risk?
Yes. Jailbreaking bypasses built-in protections, increases exposure to malware, and can void security guarantees.
Jailbreaking weakens security, best avoided.
Quick Summary
- Prioritize timely OS updates on any device
- Limit app permissions and install from trusted sources
- Enable MFA and hardware-backed security where possible
- Understand that platform openness affects risk—context matters
- Regularly review security settings and backups